Cloak
Evading censorship by tunneling Tor traffic over WebRTC video streams
Obfuscation
Cloak turns Tor traffic into WebRTC video
High-Throughput
Offers over 1Mbps upload / download speed
Traffic-Analysis Resistance
Undetectable by censors using machine learning-based analysis of network flows.
Trusted Bridge Infrastructure
Trustworthy bridge infrastructure for enabling anyone to use Cloak.
About Cloak
The Tor anonymity network is widely used by journalists and whistleblowers to safely share sensitive
information in countries where they would otherwise endure retaliation. This has led repressive regimes
to block access to Tor by employing extensive network-level interference techniques. This project aims
to design and implement Cloak: a new technology that allows Internet users to circumvent Tor blocking
and give users unrestricted access to Tor while, simultaneously, preventing these communications from
being detected by government-controlled ISPs. Concretely, Cloak will consist of a new Tor pluggable
transport (and surrounding ecosystem) that will establish covert channels between Tor browsers and Cloak
bridges, which act as proxies to the free Tor network. Cloak will set up these covert channels by
piggybacking Tor traffic on the video streams of widely-used web conferencing services based on WebRTC
technology, e.g., meet.jit.si. Thus, under the guise of a regular video call, users will be able to freely
and stealthily access services like SecureDrop without being blocked or detected. Cloak will thereby
help to expand open access to information across the world.
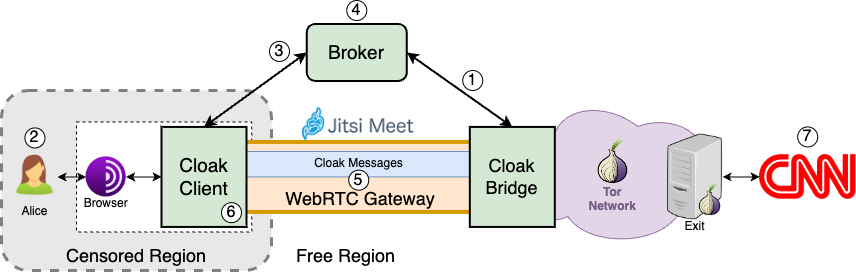
The above figure presents Cloak's overview. In the depicted scenario, a user living inside a censored
region, Alice, would like to access CNN's website despite it being blocked by the government. Alice will
take advantage of the fact that Jitsi Meet is still available to her and use Cloak to access this otherwise
restricted service. The sequence of events that must take place for Alice to be successful is as follows: 1)
a Cloak Bridge operating in a free region registers its availability with a Broker; 2) Alice uses a browser
configured to use the Tor Network (eg. Tor Browser) via the Cloak pluggable transport to request cnn.com;
3) the Cloak client running on Alice's machine generates a random chatroom ID to use with Jitsi Meet; 4)
the chatroom ID is relayed to the Broker, who then finds an available Bridge and shares this ID with it; 5) a
WebRTC video call is established between Alice and the Bridge via Jitsi Meet using Alice's chatroom; 6) all
requests destined for cnn.com are forwarded to the Tor Network through the WebRTC gateway, allowing 7)
Alice's access to CNN.
Demo
Project Stages
Cloak's development stages, both completed and ongoing.
Stage 1 - Retrofit Protozoa's protocols into Cloak
Adapt Protozoa's tunneling protocols to suit the specific needs of Tor traffic.
Update Protozoa's protocols to the latest WebRTC version and Video Codecs.
Stage 2 - Calibrate Protozoa for tunneling Tor traffic
Fine-tune Protozoa's covert channel protocols to reduce the performance penalty on Tor circuitry.
Evaluate Cloak's resistance against traffic analysis.
Stage 3 - Help users to find Cloak bridges through a Broker
Trustworthy and reliably advertising of Cloak bridges using a broker.
Prevent censors from easily detecting and blocking bridges.
Connect cloak clients and brokers.
Stage 4 - Maintain a trusted Cloak bridge infrastructure
Deploy and maintain a variety of geographically dispersed Cloak bridges.
Efficiently manage bridges' availability over multiple alternate WebRTC services.
Stage 5 - Headless and automated video call components
Fully automate the process of launching the browser and starting the video call.
Run the browser in headless mode (without a graphical interface).
Stage 6 - Incorporate into Tor ecosystem
Incorporate Cloak into the Tor Browser ecosystem.
Collaborate with Tor's Anti Censorship Team to get Cloak deployed.
Contact
Reach out to us!
Location:
INESC-ID Lisboa
Rua Alves Redol, 9
1000-029, Lisboa, Portugal
Email:
fsilva@dpss.inesc-id.pt


